'Robust ICT service delivery in practice with risk-based (modern) access'
Robust ICT service delivery in practice
Looking back recording Robust ICT services in practice
If a company's service (e.g. an Internet or VPN service) goes down unexpectedly, it often creates a bad image with customers and investors. Practice shows that avoiding outages is not easy.
Throughout the life cycle of a service, from start to finish, there are many hurdles to overcome. It starts with a business case and a well-thought-out design.
This is an important phase that can prevent or minimise many future problems. Once the service is then built and 'live', a long-term phase of growth, expansion and change begins.
During this phase, many problems of various kinds, impact and complexity can arise. This talk will address and number of key hurdles that need to be overcome to ensure reliable/robust service delivery. A number of practical examples will highlight the importance of this.
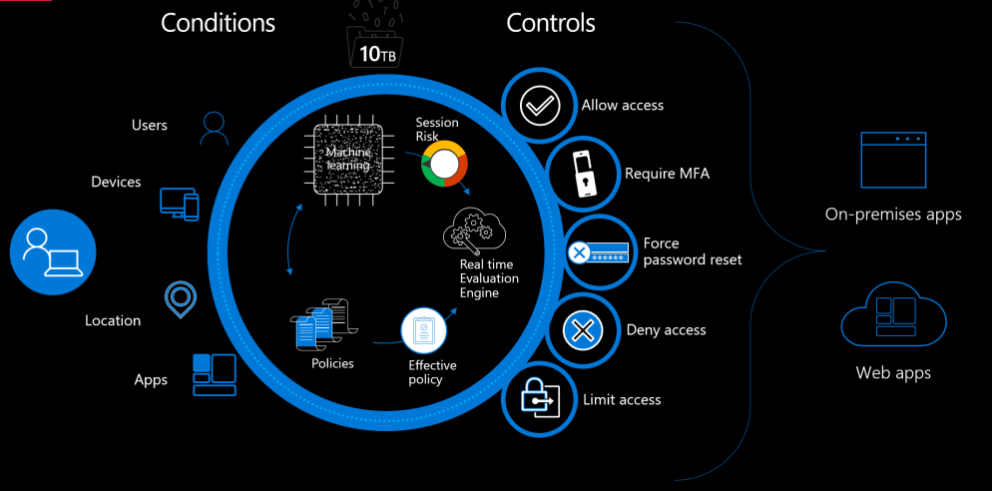
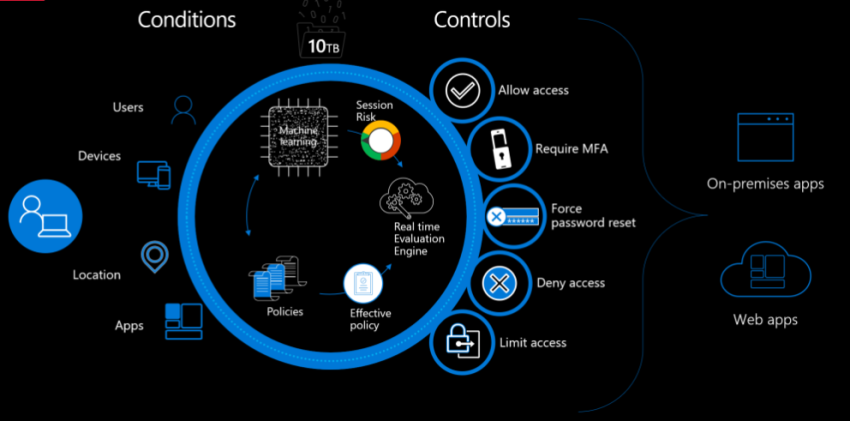
Zero Trust Security
Zero Trust is a security model for businesses to more effectively adapt to the complex information environment, embracing the hybrid workplace for people, to better protect devices and data, in any location, at home, at work and in the cloud.
Defining the Zero Trust security model with the following principles:
-
Authentication and Authorisation: Express authentication Always authenticate and authorise based on all available data points, including user identity, location, device status, service or workload, data classification and anomalies.
-
Network segmentation: Use access with minimal authorisation Restrict user access with customisable policies for timely and sufficient access (JIT/JEA) and data protection to protect both data and productivity.
-
Monitoring Assume a leak Minimise and impact and access segments. Verify end-to-end encryption and use analytics to gain insight, promote threat detection and improve defence.
Zero Trust explained
Instead of assuming that everything behind the firewall is secure, the Zero Trust model assumes that there is a leak and verifies every request as if it came from an open network.
Regardless of where the request comes from or what source it consults, Zero Trust teaches us to "never trust, always verify". Every access request is fully verified, authorised and encrypted before access is granted.
To minimise lateral movement, micro-segmentation and minimal authorisation policies are applied. Comprehensive intelligence and analytics are equipped to detect and respond to anomalies in real time.
Areas for Zero Trust protection
-
Identities: Verify and protect any identity with strong authentication access across your entire digital environment.
-
Endpoints: Insight into devices, which access the network. Check compliance and status before access is granted.
-
Apps: Discover hidden IT software, check for proper app permissions, distribute access based on real-time analytics, monitor and manage user actions.
Speakers:
First Presentation
Abstract: 'Robust ICT services in practice'
- Alexander Peek
Speaker bio

Alexander Peek is a global product manager with more than 25 years of experience in IT and B2B telecoms. At Colt Technology Services, he started as engineering manager for Colt Netherlands where he expanded the Colt network to include fibre networks and data centres in the Netherlands. He then served as product manager responsible successively for Access services, Global Enterprise services and setting up a new service for trading on global exchanges. This provided a wealth of knowledge on designing and managing reliable services.
Second Presentation
Abstract: 'Risk-Based (Modern) Access Zero Trust Architecture'
- Sacha Latuheru is Senior Consultant Capgemini Cloud Infrastructure Services.
Speaker bio
Sacha Latuheru is an experienced Workplace Architect at Capgemini and has a strong affinity for, and good knowledge of, Microsoft Cloud products. As Solution Architect on the Stedin account, he contributes, with the development of a modern working environment, to the energy transition that Stedin is full of. Before making the switch to ICT, Sacha served as a professional soldier in a combat role for 13 years and has been deployed several times to the former Yugoslavia, Cambodia and Zaire, among others.